It’d begin with a good friend’s textual content message asking why you despatched them a bizarre hyperlink, or it could possibly be a notification out of your financial institution about a purchase order you by no means made.
At that second of panic, it is simple to really feel helpless. Your telephone holds funds, images, paperwork, and every day communications, so a compromised telephone feels deeply private.
Take a deep breath. That is an emergency first-aid plan that each Android and iOS customers can use.
Comply with these six steps to diagnose the difficulty, isolate your telephone, safe your accounts, take away the menace, and handle the aftermath. You’ve got received this.
6
Indicators your telephone could be compromised
Do not wipe your system but. Search for proof first. Attackers and their malware not often keep invisible. They go away traces in efficiency, settings, and account exercise.
This is what to look at for, grouped into three classes. If a number of seem throughout classes, cease investigating and act.
Unusual messages and suspicious account exercise
The primary indicators of compromise typically seem in your on-line accounts, not on the telephone. Pals or household could report unusual messages or texts out of your quantity.
These typically embrace suspicious hyperlinks, a standard means malware spreads. You may additionally see unfamiliar calls or texts in your logs. Attackers can use your telephone to position premium-rate calls or ship spam.
Look ahead to sudden account lockouts or surprising password reset prompts, which may generally embrace a flood of two-factor authentication codes you did not request.
These are clear indicators that somebody is making an attempt to take over your accounts.
Battery drain and warmth you may’t clarify
Background malware constantly consumes system sources. Signs are sudden battery drain, warmth when the telephone is idle, and poor efficiency.
A telephone that when lasted all day could drop to low battery by noon with the identical utilization.
Warming throughout charging or gaming is regular, however persistent idle warmth alerts fixed CPU exercise from hidden processes.
You may additionally discover sluggish app launches, freezes, or surprising restarts. Malware hogs reminiscence and processing energy, leaving much less for reputable apps and inflicting extra crashes.
Pop-up adverts, unfamiliar apps, and unexplained information use that time to adware
A hacked telephone works for the attacker, and this exercise typically seems in your information utilization and residential display screen. An unexplained spike in information use is a key warning signal.
Malware communicates with its operator by exfiltrating information and fetching instructions that devour cellular information. One other clue is unfamiliar apps you did not set up.
Some producers preinstall apps, however any app you do not acknowledge could possibly be spyware and adware or adware.
A sudden surge of pop-up adverts, even whenever you aren’t shopping, strongly suggests adware on the system.
5
Fast steps to isolate a compromised telephone
Restarting your telephone is a sensible first step whenever you see suspicious exercise. This clears energetic reminiscence and stops background processes, which may interrupt malware that depends upon a operating session, and forces apps to reload cleanly.
It won’t take away persistent infections that reinstall at startup, so deal with it as a short lived measure, not a remedy.
Activate Airplane Mode for stronger protection. Airplane Mode disconnects mobile, Wi-Fi, and Bluetooth.
The attacker can now not ship instructions or siphon information in actual time, and buys you time to run a safety scan, change passwords, or restore the system.
4
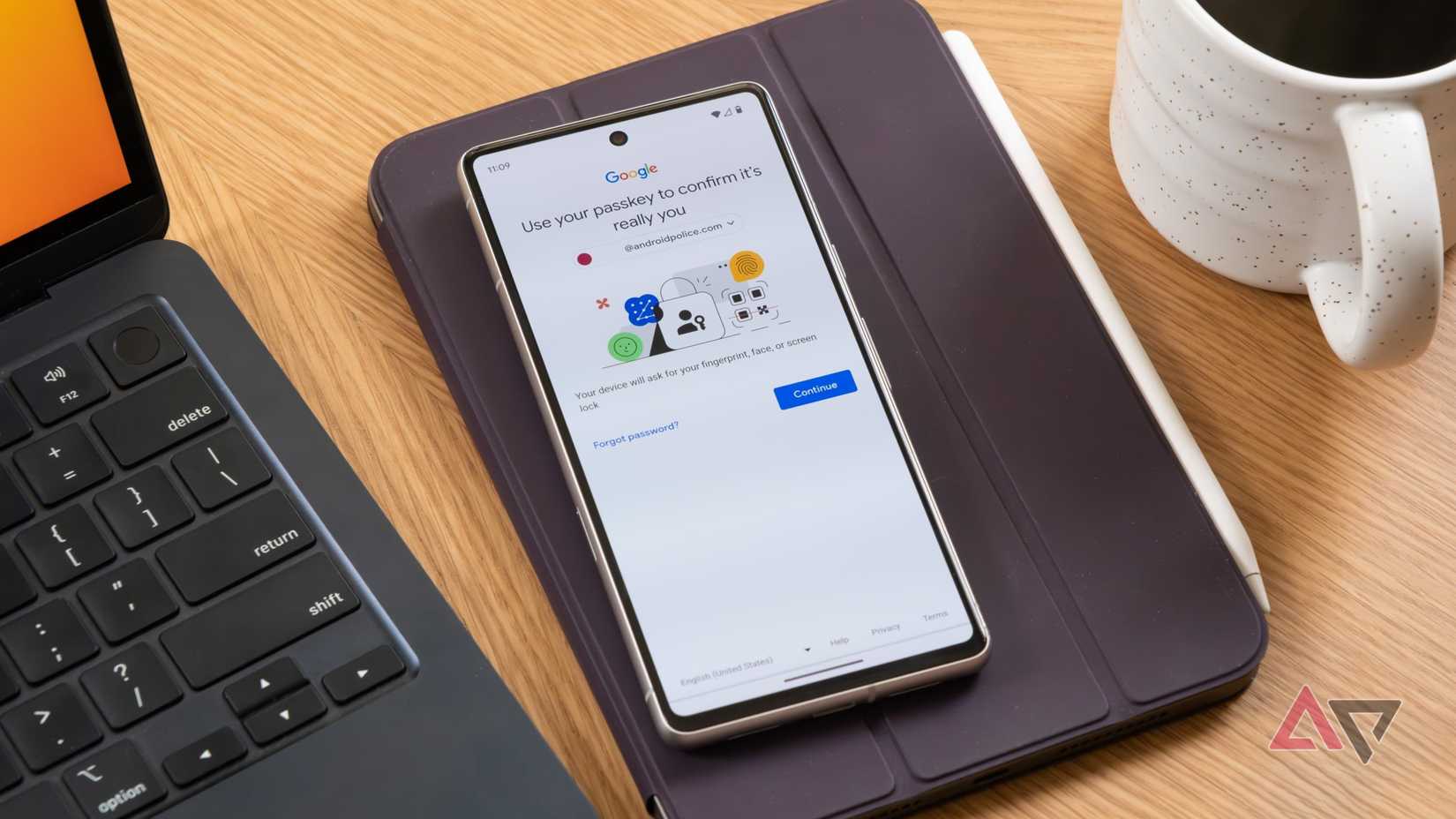
Safe your core accounts
Securing your core accounts is the only most necessary step after a hack. Use a separate, trusted system comparable to a laptop computer, work pc, or a member of the family’s pill.
Don’t change passwords on the compromised telephone. Adware or a keylogger might seize every little thing you kind and hand it to the attacker.
Begin together with your major e-mail account, as it is the restoration key for many companies.
Subsequent, safe your Apple ID or Google account, which manages backups, app retailer purchases, and cloud information.
Then replace your banking and monetary accounts, adopted by your most important social media accounts, to stop impersonation.
Activate two-factor authentication on every account as you go. This sequence retains your new credentials secure and helps lock out attackers.
Use an authenticator app comparable to Google Authenticator, Microsoft Authenticator, or Authy as a substitute of SMS codes, that are susceptible to SIM swap assaults.
3
Learn how to again up recordsdata with out spreading malware
Earlier than wiping your telephone, manually save important recordsdata. The purpose is to protect irreplaceable information like images, movies, and paperwork with out introducing malware in the course of the reset.
Add them manually to your cloud account. Skip full system backups. Restoring can deliver the an infection again if malware is embedded in a system backup.
Guarantee your cloud storage is secured with sturdy, distinctive passwords and two-factor authentication.
Use a focused copy as a substitute. It’s also possible to copy recordsdata on to a pc with a USB cable. Nevertheless, if the telephone is hacked, malware might unfold to the pc.
For those who use this technique, switch solely media (not system folders or apps). Since these are media recordsdata and never executables, the danger of malware is decrease. Scan the recordsdata with antivirus software program earlier than opening them.
2
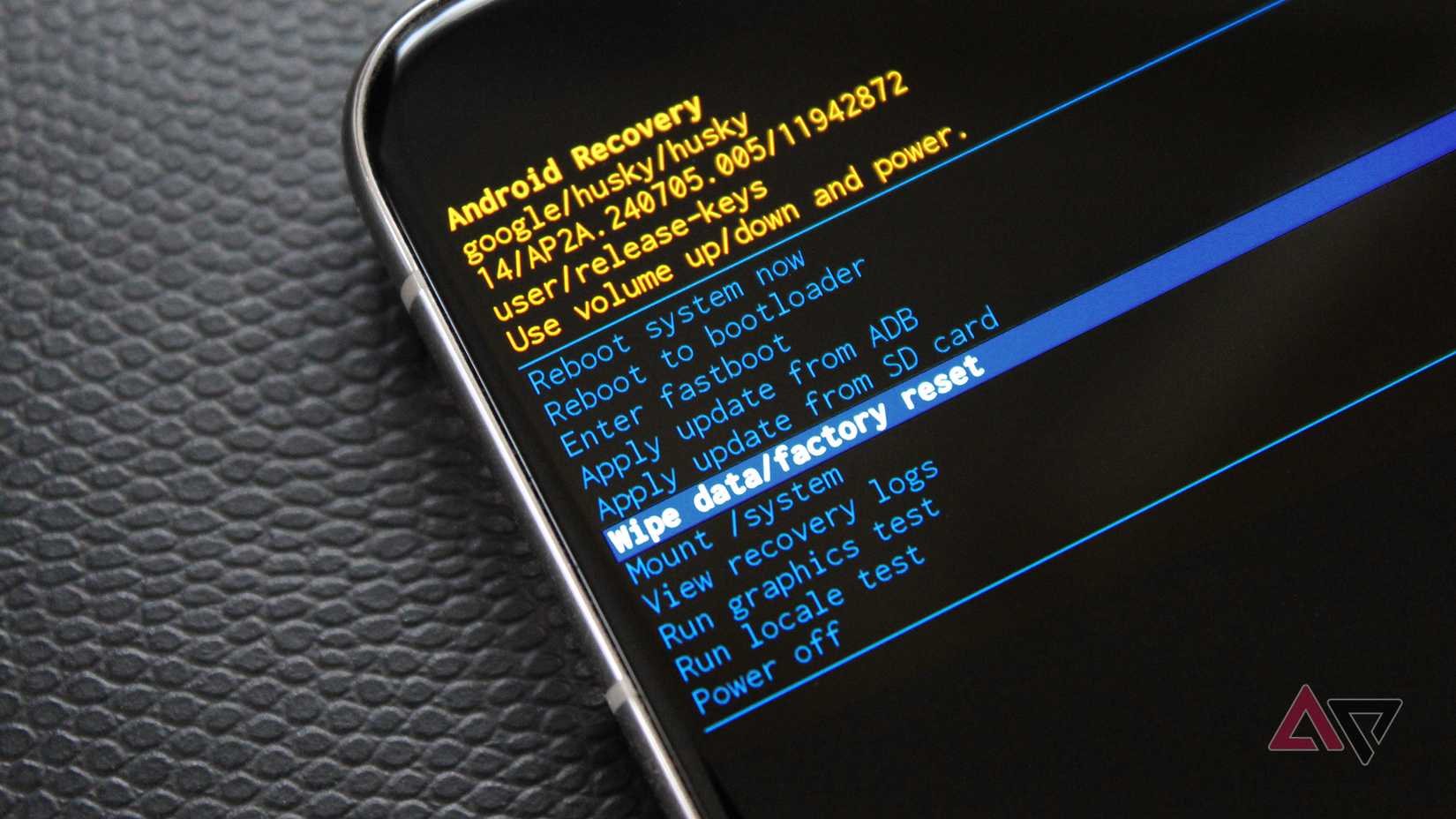
A manufacturing facility reset is your strongest protection
A manufacturing facility reset is the ultimate step in reclaiming your system. It erases apps, settings, images, messages, and all different information after which restores the telephone to manufacturing facility settings.
That is essentially the most dependable option to take away malware as a result of it resets your entire surroundings relatively than deleting a suspicious app or file.
Uncommon, superior threats can survive a reset by hiding in firmware, the bootloader, or the restoration partition. These rootkits or bootkits require reflashing the firmware.
A manufacturing facility reset is ample for nearly all frequent malware. After the reset, don’t reinstall apps from untrusted sources. Restoring the identical malicious app will reinfect the system.
1
Monitoring accounts for lingering threats
End by managing the fallout and guarding towards ongoing threat. Even after you take away malware, attackers should still maintain private or monetary information, so keep proactive.
Contact your financial institution and card issuers to alert their fraud groups. Ask them to observe your accounts and advise on replacements.
Inform your contacts that your telephone was compromised and to disregard any uncommon messages.
Overview your statements recurrently for the following few months and flag any small, unfamiliar prices.
For those who suspect fraud or identification theft, report it to your financial institution and your native shopper safety or cybercrime unit.
These steps will preserve your accounts safe and restrict additional injury.
Classes realized from surviving a hack
Recovering from a hack is worrying, nevertheless it has a profit. You simply ran a real-world hearth drill. The expertise reveals the way you reply underneath stress and why cybersecurity habits matter.
Make prevention a routine. Overview your safety settings recurrently to maintain them present and efficient. Again up solely what it’s essential to restrict publicity.
Be selective about what you click on, obtain, and set up, since many assaults begin with a single faucet on a malicious hyperlink or app.