Nothing hampers up-and-coming developments as a lot as excessive recognition. Android, the world’s commonest working system, provides unhealthy actors a possibility to power malicious code on customers, usually with out their data. Almost twenty years after its beginning, the OS integrates safeguards to reduce malware hazards. Together with instruments like safe password managers and VPNs, your Android telephone provides loads of methods to bolster your safety.
It wasn’t at all times this manner. Varied exploits over time have leveraged vulnerabilities in Android, the Google Play Retailer, and third-party apps to extract delicate knowledge or rack up unapproved expenses. In some circumstances, researchers caught the incursion earlier than important injury was carried out, and a few hacks stay noteworthy attributable to their affect on app growth and supply frameworks. These are their tales.

Associated
7 privacy-focused Android apps I take advantage of to maintain my knowledge safe
Important Android apps to lock down your knowledge
6
FakePlayer opens the floodgates
Android malware will get an inauspicious begin
Supply: Unsplash / Wikimedia Commons
Two years after Android’s launch, its increasing consumer base enticed menace actors sufficient to develop a focused worm. The primary broadly publicized Android malware, designated SMS.AndroidOS.FakePlayer.a, posed as a video participant however began firing off unauthorized textual content messages to premium numbers, costing customers a number of {dollars} per stream of messages.
FakePlayer ran on easy code, and it is inconceivable to quantify how a lot injury it did. Three extra variants surfaced over the subsequent yr with various complexity and assault vectors and roughly the identical aim: siphon cash from unknowing customers to corporations working with malware distributors.
The primary well-known assault may not compete with big-money ransomware by way of headline-worthy monetary affect. Nonetheless, it marks the start of the onslaught of malicious code focusing on Android customers, with dozens of exploits arising over the next yr. It marked the start of an arms race between thieves and builders. It took years for programmers to achieve the higher hand within the battle, because of FakePlayer and different notable discoveries.
5
StageFright offers beginning to recurring safety patches
When unhealthy actors push the business ahead
Supply: Android Police
An Android Open Supply Mission code library referred to as libstagefright comprises numerous media playback codecs and lives deep contained in the software program’s code. Profiting from essential holes in how the library interacted with reminiscence, it probably allowed zero-click exploits, or malware that may activate with out customers putting in or tapping something suspicious. It reportedly put a majority of Android gadgets in danger.
Safety agency Zimperium’s July 27, 2015, announcement of StageFright’s discovery despatched shockwaves all through the business. Earlier than then, safety updates arrived in refined type alongside minor OS updates however weren’t an business focus, not to mention any telephone producer’s promoting level. The potential exploit impressed Android’s month-to-month safety patches and the bulletins outlining them. After addressing StageFright, builders moved on to shut numerous holes that enabled its existence.

Associated
6 methods to inform in case your Android telephone has malware
Indicators your Android telephone has been contaminated
The well-known hack made large waves. It pushed code frameworks towards compartmentalization, proscribing apps’ privileges to solely what they should work appropriately and disallowing rogue software program from accessing delicate knowledge. The brand new focus impressed enhancements like sanitizing reminiscence entry to restrict buffer overflows, particular additions like Management Circulation Integrity, and fortifications to protections like tackle area format randomization. These, and different modifications below the hood, can forestall contaminated gadgets from being totally compromised.
StageFright will perpetually maintain a spot within the annals of Android safety because of its outsize affect on software program growth and safety analysis. A decade later, it is unclear if the “Worst Android vulnerability in cellular OS historical past” was ever exploited in the actual world, nevertheless it’s nonetheless essentially the most well-known.
4
HummingBad earns huge bucks for months
A respectable firm, Yingmob, and its illegitimate practices
Supply: @Universeice by way of X/Twitter
Not all malware campaigns have pleased endings. The StageFright revelation did not remove the specter of malware, and a yr later, a startling crime ring emerged. The HummingBad malware marketing campaign reportedly garnered $300,000 per thirty days whereas Verify Level researchers (PDF) infiltrated the group accountable.
The engineers outlined how the software program tried and obtained root entry on numerous gadgets. An estimated 85 million gadgets have been uncovered, with some 10 million falling sufferer to the marketing campaign. After a compromised app was put in, it compelled repeated behind-the-scenes set up of extra malicious software program. The apps would then inject numerous popup adverts and use darkish patterns and different illegitimate strategies to get clicks.
HummingBad did not steal identities or cash from its victims, however the huge capabilities of its root entry may have. It affected hundreds of thousands of customers’ expertise and turned the main Android malware months after its discovery.
3
CovidLock and opportunistic assaults
Placing when harassed customers least anticipate
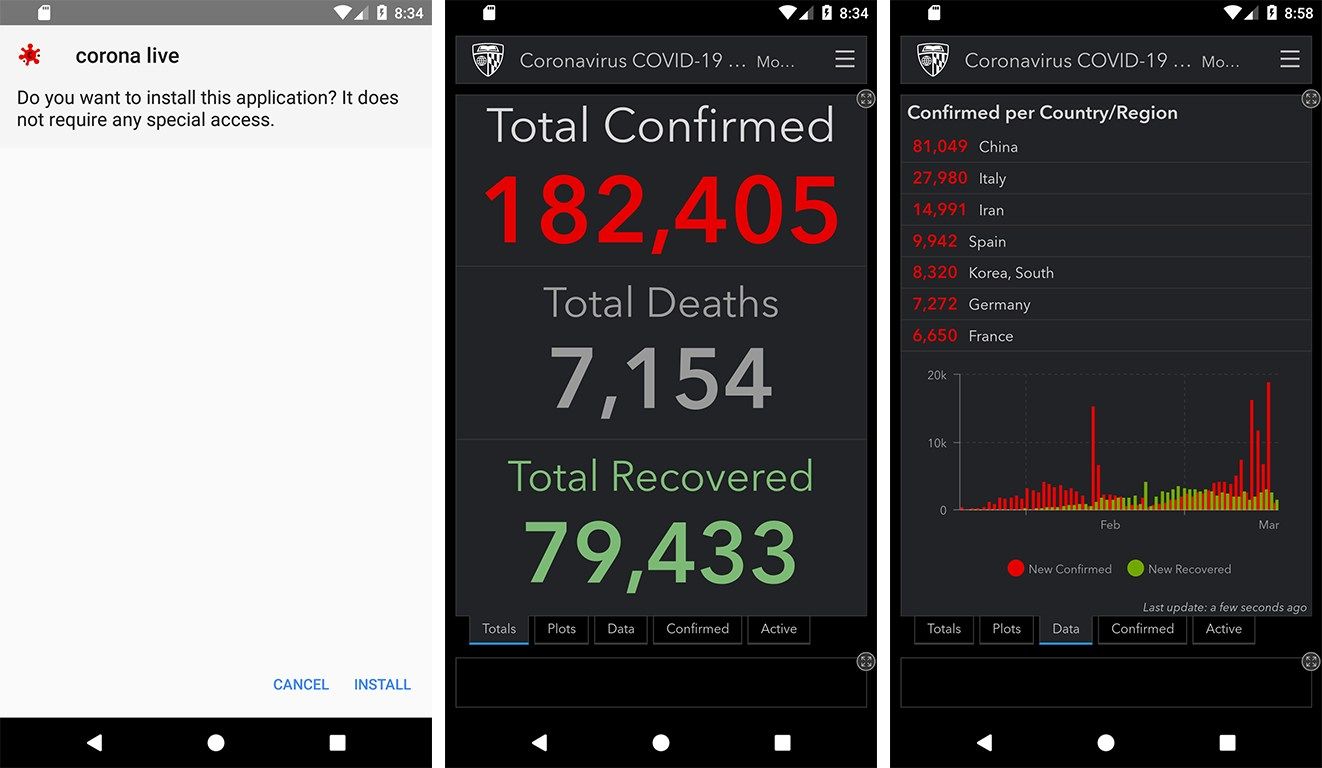
Supply: Lookout Analysis
Extra Covid-centric rip-off apps, just like the above Corona Dwell 1.1, emerged across the identical time.
Unscrupulous teams love profiting from worrying information like international well being emergencies. That occurred in 2020 when CovidLock hit the scene and promised to tell shoppers about staying secure from COVID-19. It marketed an infection warmth maps and numerous statistics however locked affected gadgets till house owners paid a ransom.
Failing to lock telephones with passwords led to most vulnerabilities, which proved the common consumer was nonetheless studying about safety 5 years in the past. It additionally underlined how attackers reap the benefits of these in traumatic medical conditions. Risk vectors like Remedy for Diabetes and different health-related apps threaten to show data like IP addresses and topic customers to invasive, unlawful adverts. Ultimately, ZScaler researchers uncovered a repair to treatment affected gadgets.
2
xHelper exemplifies improved hacking methods
Exploits have come a great distance, child
Supply: Pixabay
Whether or not it is injecting popup adverts or stealing delicate data, malicious code wants to stay round your system lengthy sufficient to do injury. There is not any higher method to make sure longevity than to make an app inconceivable to uninstall. That is how xHelper continued fleecing customers into downloading pointless apps, driving illicit income via pay-per-install initiatives.
xHelper stymied researchers for a couple of yr earlier than Malwarebytes outlined the removing course of, and a Kaspersky researcher uncovered the malware’s strategies two months later. Its novel implementation and the comparatively refined design of malware contemporaries like CovidLock highlighted how far menace actors had come over the previous dozen years.
Serving to governments take what’s yours
An Israeli cyber-intelligence firm referred to as NSO Group Applied sciences launched Pegasus in 2021, claiming to offer “approved governments with know-how that helps them fight terror and crime.” The long-running instrument has allowed governments worldwide to spy on people, together with human rights activists and journalists.
The highly effective hack targets iOS and Android and goes to nice lengths to cover its exercise and existence. Fairly than assault a single exploit, it employs a posh suite of methods using numerous vulnerabilities. This type of software program requires a workforce {of professional} builders and loads of funding. Pegasus has each.
The upside of a instrument like Pegasus is that common customers do not have something to fret about. Whereas governments can possible spy on our each transfer, intensive surveillance prices rather a lot, and most customers aren’t that essential. The worrying a part of a product like Pegasus is that it has the backing to proceed threatening customers. Whereas it’d by no means goal you, a robust, undetectable, root-access hack of legal professionals, lawmakers, and human rights advocates is not nice for society.
Staying secure from Android malware at the moment
Supply: Pixabay
The indefatigable efforts of builders at Google, particular person producers, and software program corporations have led to a rise in malware detection and a lower in its distribution. That may be excellent news, besides ransomware teams made report earnings in 2024. As smartphones change into more and more built-in into private {and professional} lives, understanding how malware threatens gadgets is extra essential than ever.
After a lot refinement, Android does job mitigating threats on the {hardware} and software program degree at the moment. Human conduct is, and at all times will likely be, the weak level in digital safety. Whereas a safety patch will cease some malicious software program in its tracks, exploits can maneuver round protections by convincing customers to offer entry to high-level permissions.

Associated
Android safety patches do not matter as a lot as you assume
You are not that screwed once they cease
Widespread methods, resembling phishing, usually lead to customers willingly providing login particulars. It is essential to keep away from unfamiliar hyperlinks and PDF information. By no means present personal data in response to an e-mail or textual content message outreach, and at all times navigate to a service of your individual accord to ensure you’re not being defrauded. Solely the suitable degree of consideration can totally shield you from ransomware and theft. Possibly, sometime, Android can launch a safety patch for the human situation.